The Supermicro Security Center is the established source for product security updates and information from Supermicro, a global leader in enterprise computing, storage, networking, and green computing technology. We strive for continuous improvement in our security practices.
The security of our customers is a top priority; hence we have put measures in place to safeguard the operation of your Supermicro servers and storage systems. Servers and storage systems as they exist today are becoming more versatile yet more complex with the need to be secured. With threat actors, Supermicro is developing defense mechanisms to protect users and customers and thus bring our security knowledge to the highest in the industry. Supermicro recognizes that customers expect to deploy products that meet high-security standards; therefore, our response is designed for the highest level of protection.
Supermicro recommends that you follow security best practices, including keeping your operating system up-to-date and running the latest versions of firmware and all software.
Lifecycle Cyber Security Product Protection
Supermicro offers three server products made exclusively in the US. By centralizing manufacturing in US factories, system integrity is preserved. These “Made in the USA” products reduce the opportunity for foreign cybersecurity intrusion and are available for customers worldwide. To learn more about this program, go to the Made in the USA solution page.
Supermicro strictly manages cybersecurity practices throughout our entire supply chain system, to include a broader “cradle to grave” approach to keeping our products secure from sourcing and production, through operation, to a natural end of life.
Supermicro’s best practices are designed to meet its product security requirements that are supported by rich security functionality and features. These features assure customers that Supermicro's products meet industry security standards.
Last Updated:
Supermicro regards the security of your data center with the highest importance. Supermicro is providing a list of standards and specifications for the newly-released X14/H14 as well as X13/H13/R13 and X12/H12 families of servers and storage systems. These built-in capabilities will serve as a guideline for establishing secure operations within your data center. Review the list below.
| Category | Security Specifications | Intel X14 Products | AMD H14 Products | Intel X13 Products | AMD H13 Products | Ampere R13 Products1 | Intel X12 Products | AMD H12 Products |
|---|---|---|---|---|---|---|---|---|
| Hardware | Silicon Root of Trust | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ |
| Chassis Intrusion Protection | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| Trusted Platform Module (TPM) 2.0 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ||
| BMC TPM1 | ✔ | ✔ | ✔ | ✔ | ||||
| Intel Boot Guard | ✔ | ✔ | ✔ | |||||
| Intel® Software Guard Extensions (Intel® SGX)1 | ✔ | ✔ | ✔ | |||||
| AMD Secure Processor | ✔ | ✔ | ✔ | |||||
| AMD Secure Memory Encryption (SME) | ✔ | ✔ | ✔ | |||||
| AMD Secure Encrypted Virtualization (SEV) | ✔ | ✔ | ✔ | |||||
| BIOS/BMC | Secure Boot | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ |
| Secure Drive Erase | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| Secure Flash | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| Secure Firmware Updates | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| Cryptographically signed firmware | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| Secure Redfish API3 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| Password Security | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| USB dynamic enable/disable | ✔ | ✔ | ||||||
| HDD Password | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| BMC Unique Password | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| Automatic Firmware Recovery | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| Anti-rollback | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ||
| Runtime BMC Protections | ✔ | ✔ | ✔ | ✔ | ||||
| System Lockdown | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ||
| Supply Chain Security: Remote Attestation | ✔ | ✔ | ✔ | ✔ | ||||
| Drive Key Management (Super-Guardians) | ✔ | ✔ | ✔ | ✔ | ✔ | |||
| IPMI 2.0 User Locking | ✔ | ✔ | ✔ | ✔ | ✔ | |||
| Security State Monitoring | ✔ | ✔ | ✔ | ✔ | ||||
| Security Protocol and Data Model (SPDM) Management2 | ✔ | ✔ | ✔ | ✔ | ||||
| Standards | NIST SP 800-193 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | |
| NIST SP 800-147b | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ||
| NIST SP 800-88 | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ | ✔ |
Notes:
- Certain features may not apply to all products.
- 1 On select models and configurations
- 2 Planned on Q4 CY2024
- 3 TLS v1.2 / v1.3 supported. RMCP+ Cipher Suite3 / 17 supported
The Baseboard Management Controller (BMC) provides remote access to multiple users at different locations for networking. BMC allows a system administrator to monitor system health and manage computer events remotely. BMC is used with an (Intelligent Platform Management Interface) IPMI Management utility which makes it possible to control and monitor servers centrally. BMC has a wide range of security features that address customer requirements.

Security Best Practices for managing servers with BMC features enabled in Datacenters
Learn about BMC Security Best Practices
Dynamic System Verification Leveraging the Attestation Process
Detect any changes in the hardware and firmware using system attestation
Cryptographically Signed BMC Firmware
Learn about Security functionality to cryptographically sign the BMC Firmware and BIOS
BMC Unique Password Security Feature
Learn how to benefit from BMC Unique Password
AMD Security Bulletin AMD-SB-7054, April 2026
Supermicro is aware of the security issue where an incorrect use of LocateProtocol Service could result in privilege escalation from Ring 0 to System Management Mode (SMM), potentially resulting in arbitrary code execution. AMD released mitigations for this vulnerability. This vulnerability affects BIOS in Supermicro H12, H13, and H14 products.
- CVE-2025-54502
AMD Security Bulletin AMD-SB-3034, April 2026
Supermicro is aware of the security issue where a privileged attacker may alter Memory Mapped I/O (MMIO) routing configuration registers, potentially compromising SEV-SNP guest memory integrity. AMD released mitigations for this vulnerability. This vulnerability affects BIOS in Supermicro H12, H13, and H14 products.
- CVE-2025-54510
AMD Security Bulletin AMD-SB-3016, April 2026
Supermicro is aware of the security issue where an internal security audit found a potential vulnerability that could allow a malicious hypervisor to direct the IOMMU to write into Secure Encrypted Virtualization-Secure Nested Paging (SEV-SNP) guest memory. AMD released mitigations for this vulnerability. This vulnerability affects BIOS in Supermicro H12, H13, and H14 products.
- CVE-2023-20585
Intel Platform Update (IPU) Update 2025.3 Part 2, March 2026
This update applies to the X11, X12, and X13, X14 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-01234 – 2025.3 IPU - UEFI Reference Firmware Advisory
AMD Security Bulletin AMD-SB-7059, February 2026
Supermicro is aware of the security issue where it may be possible for a guest virtual machine (VM) to cause a crash of a host system. AMD released mitigations for this vulnerability. This vulnerability affects BIOS in Supermicro H11, H12, H13, and H14 products.
- CVE-2023-31364
Intel Platform Update (IPU) Update 2026.1, February 2026
This update applies to the X11, X12, and X13, X14 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-01314 – 2025.4 IPU - Intel® TDX Module Advisory
- INTEL-SA-01315 – 2026.1 IPU - Intel® Chipset Firmware Advisory
- INTEL-SA-01396 – 2026.1 IPU - Intel® Processor Firmware Advisory
- INTEL-SA-01397 – 2026.1 IPU - Intel® Trust Domain Extensions (Intel® TDX) module Advisory
AMD Security Bulletin AMD-SB-3023, February 2026
Supermicro is aware of the potential vulnerabilities in AMD EPYC™ Processor platforms that affect I/O Memory Management Unit (IOMMU), AMD Secure Encrypted Virtualization – Secure Nested Paging (SEV-SNP), and other platform components that were found during audits performed internally and by third parties. This vulnerability affects BIOS in Supermicro H11, H12, H13, and H14 products.
- CVE-2025-52533, CVE-2025-29950, CVE-2024-36355, CVE-2025-29939, CVE-2025-0012, CVE-2025-52536, CVE-2024-21961, CVE-2025-29948, CVE-2024-21953, CVE-2025-29952, CVE-2025-52534, CVE-2025-54514, CVE-2025-48517, CVE-2025-0031, CVE-2024-36310, CVE-2025-29946, CVE-2025-48514, CVE-2025-0029, CVE-2025-48509
Microsoft Secure Boot CA 2011 End-of-Life: Transition to 2023 Certificates
Microsoft’s Secure Boot CA 2011 certificates expire in June 2026, after which devices relying only on them will stop receiving security updates for the Windows Boot Manager and Secure Boot components, increasing bootkit vulnerability risk. Microsoft is transitioning to new 2023 certificates; Supermicro has released supporting BIOS updates, and users should keep Secure Boot enabled, install the latest BIOS/firmware, and apply all updates—no immediate action is needed for most systems as the transition will occur automatically on supported devices.
View detailsVulnerabilities in Supermicro BMC firmware, January 2026
Several security issues have been discovered in select Supermicro motherboards. These issues affect Supermicro BMC Firmware.
- CVE-2025-12006
- CVE-2025-12007
AMD Security Bulletin AMD-SB-3027, January 2026
Supermicro is aware of the security issue where Stale RLB Entry could allow Secure Nested Paging (SNP) active virtual central processing units (vCPUs) to reuse TLB entries from other virtual machines (VMs), potentially compromising data integrity. AMD released mitigations for this vulnerability. This vulnerability affects BIOS in Supermicro H12 and H14 products.
- CVE-2025-29943
Vulnerabilities in Supermicro BMC firmware, November 2025
Four security issues have been discovered in select supermicro boards and CMMs. These issues may affect Supermicro BMC Firmware.
- CVE-2025-7623
- CVE-2025-8076
- CVE-2025-8404
- CVE-2025-8727
AMD Security Bulletin AMD-SB-3029, November 2025
Supermicro is aware of the security issue where Stale RLB Entry could allow Secure Nested Paging (SNP) active virtual central processing units (vCPUs) to reuse TLB entries from other virtual machines (VMs), potentially compromising data integrity. AMD released mitigations for this vulnerability. This vulnerability affects BIOS in Supermicro H12, H13, and H14 products.
- CVE-2025-29934
Vulnerabilities in Supermicro BMC firmware, October 2025
Several security issues have been discovered in select Supermicro motherboards and CMMs. These issues affect Supermicro BMC Firmware.
- CVE-2025-7704
AMD Security Bulletin AMD-SB-7055, October 2025
Supermicro is aware of the security issue that may cause the RDSEED instruction to return “0” at a rate inconsistent with randomness while incorrectly signaling success (CF=1), indicating a potential misclassification of failure as success. AMD released mitigations for this vulnerability. This vulnerability affects BIOS in Supermicro H13 and H14 products.
- CVE-2025-62626
AMD Security Bulletin AMD-SB-3020, October 2025
Supermicro is aware of the security issue where a malicious hypervisor could corrupt the Reverse Map Table (RMP) during Secure Nested Paging (SNP) initialization. This issue affects AMD EPYC™ 3rd, 4th and 5th Gen Processors. This vulnerability affects BIOS in Supermicro H12, H13, and H14 products.
- CVE-2025-0033
Vulnerabilities in Supermicro BMC firmware, September 2025
Several security issues have been discovered in select Supermicro motherboards. These issues affect Supermicro BMC Firmware.
- CVE-2025-7937
- CVE-2025-6198
Intel Platform Update (IPU) Update 2025.2 Part 2, August 2025
This update applies to the X11, X12, and X13, X14 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-01245 – 2025.2 IPU - Intel® TDX Module Advisory
- INTEL-SA-01249 – 2025.2 IPU - Intel® Processor Stream Cache Advisory
Intel Platform Update (IPU) Update 2025.3, August 2025
This update applies to the X11, X12, and X13, X14 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-01280 – 2025.3 IPU - Intel® Chipset Firmware Advisory
- INTEL-SA-01312 – 2025.3 IPU - Intel® TDX Module Advisory
- INTEL-SA-01313 – 2025.3 IPU - Intel® Xeon® Processor Firmware Advisory
AMD Security Vulnerabilities, August 2025
This update applies to the H11, H12, H13 and H14 families of products powered by 1st/
- AMD-SB-4012 – AMD Client Vulnerabilities – August 2025
- AMD-SB-3014 – AMD Server Vulnerabilities – February 2025
AMD Security Bulletin AMD-SB-7029, July 2025
Supermicro is aware of the transient execution security vulnerabilities in some AMD processors. AMD discovered several side-channel attacks while investigating a Microsoft® report titled “Enter, Exit, Page Fault, Leak: Testing Isolation Boundaries for Microarchitectural Leaks”.
- CVE-2024-36348
- CVE-2024-36349
- CVE-2024-36350
- CVE-2024-36357
2025.1 IPU - Intel® Processor Advisory, INTEL-TA-01209, June 2025
Supermicro is aware of the security vulnerability where an unskilled user with user authentication via local operating system access can potentially impact availability (high) through denial of service by means of out-of-bounds read in firmware for Intel® CSME and Intel® SPS within Intel® PTT firmware.
- CVE-2025-2884
AMD Security Bulletin AMD-SB-7039, June 2025
Supermicro is aware of the security vulnerability which may allow a privileged attacker to access the Crypto Co-Processor (CCP) registers from x86 architecture. This issue affects AMD EPYC™ 1st, 2nd, and 3rd Gen Processors and select H11 and H12 generations of products.
- CVE-2023-20599
Intel Platform Update (IPU) Update 2025.2, May 2025
This update applies to the X11, X12, and X13, X14 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-01244 – 2025.2 IPU - Intel® Processor Advisory
- INTEL-SA-01247 – 2025.2 IPU - Intel® Processor Indirect Branch Predictor Advisory
2025.1 IPU - Intel® Processor Advisory, INTEL-TA-01153, May 2025
A processor event or prediction may allow incorrect operations (or correct operations with incorrect data) to execute transiently, potentially exposing data over a covert channel. Indirect branch predictions may not be fully constrained by enhanced IBRS properties and the Indirect Branch Predictor Barrier. This update applies to the X11, X12, and X13 families of products powered by Intel Xeon® and other Intel processors.
This vulnerability affects Supermicro BIOS in select H13 products. Supermicro is not aware of any public announcements or malicious use of these vulnerabilities that is described in this advisory.
- INTEL-SA-01153 – 2025.1 IPU - Intel® Processor Advisory
AMI Security Advisory AMI-SA-2025003, March 2025
Supermicro is aware of a potential vulnerability in the BIOS firmware as reported in the AMI security advisory AMI-SA202503. Aptio® V contains vulnerability in BIOS where an attacker may cause a Time-of-check Time-of-use (TOCTOU) Race Condition by local means. Successful exploitation of this vulnerability may lead to arbitrary code execution.
This vulnerability affects Supermicro BIOS in select H13 products. Supermicro is not aware of any public announcements or malicious use of these vulnerabilities that is described in this advisory.
- CVE-2024-54084
AMD Security Bulletin AMD-SB-7033, March 2025
Supermicro is aware of the security issue reported by Google® known as “AMD Microcode Signature Verification Vulnerability” which is caused by a weakness in the signature verification algorithm and the vulnerability could allow an administrator privileged attacker, the ability to load arbitrary CPU microcode patches.
- CVE-2024-36347
Intel Platform Update (IPU) Update 2025.1, February 2025
This update applies to the X11, X12, and X13 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-01139 – 2025.1 IPU - UEFI Firmware Advisory
- INTEL-SA-01152 – 2025.1 IPU - Intel® Chipset Firmware Advisory
- INTEL-SA-01213 – 2025.1 IPU - Intel® SGX Advisory
- INTEL-SA-01228 – 2025.1 IPU - 13th and 14th Generation Intel® Core™ Processor Advisory
AMD Security Vulnerabilities, February 2025
This update applies to the H12 and H13 families of products powered by 1st/
- AMD-SB-4008 – AMD Client Vulnerabilities – February 2025
- AMD-SB-3009 – AMD Server Vulnerabilities – February 2025
AMD Security Bulletin AMD-SB-7028, February 2025
Supermicro is aware of the System Management Mode (SMM) callout vulnerability reported by Eclypsium in the AmdPlatformRasSspSmm UEFI module supported on multiple AMD processors. This issue affects AMD EPYC™ 2nd Gen Processors and H11 and H12 generations of products.
- CVE-2024-21924
AMD Security Bulletin AMD-SB-7027, February 2025
Supermicro is aware of the two security vulnerabilities reported by Quarkslab within the AmdPspP2CmboxV2 and AmdCpmDisplayFeatureSMM UEFI modules supported on multiple AMD processors that could allow attackers to execute code within SMM(System Management Mode).This issue affects AMD EPYC™ 1st, 2nd, 3rd and 4th Gen Processors and H11, H12, and H13 generations of products.
- CVE-2024-0179
- CVE-2024-21925
AMD Security Bulletin AMD-SB-6016, February 2025
Supermicro is aware of the security vulnerabilities in Power Management Firmware (PMFW), AMD System Management Unit (SMU). This issue affects AMD H13 MI300X H13DSG-OM product.
- CVE-2024-21927
- CVE-2024-21935
- CVE-2024-21936
AMD Security Bulletin AMD-SB-6008, February 2025
Supermicro is aware of the security vulnerabilities in Power Management Firmware (PMFW), AMD System Management Unit (SMU). This issue affects AMD H13 MI300X H13DSG-OM product.
- CVE-2024-21971
- CVE-2023-20508
AMD Security Bulletin AMD-SB-3019, February 2025
Supermicro is aware of the security vulnerability reported by Google® where an administrator privileged attacker may exploit a weakness in the signature verification algorithm and load arbitrary CPU microcode patches which can result in the loss of SEV-based protection of a confidential guest.
- CVE-2024-56161
Vulnerability in Supermicro BMC IPMI Firmware, January 2025
Several security issues have been discovered in select Supermicro motherboards. These issues affect Supermicro BMC Firmware.
- CVE-2024-10237
- CVE-2024-10238
- CVE-2024-10239
AMD Security Bulletin AMD-SB-3015, December 2024
Supermicro is aware of the security issue where it may be possible to modify serial presence detect (SPD) metadata to make an attached memory module appear larger than it is, which may produce memory address aliasing. This issue affects AMD EPYC™ 3rd and 4th Gen Processors. motherboards. This vulnerability affects BIOS in Supermicro H12 and H13 products.
- CVE-2024-21944
Vulnerability in Supermicro BMC IPMI firmware, “Terrapin”, October 2024
A security issue has been discovered in select Supermicro motherboards. Terrapin vulnerability allows an attacker to downgrade secure signature algorithms and disable specific security measures. The Terrapin attack requires an active Man-in-the-Middle attacker.
- CVE-2023-48795
BIOS Vulnerabilities, September 2024
Supermicro is aware of two potential vulnerabilities in the BIOS firmware. These vulnerabilities may allow an attacker to write to SMRAM and hijack the RIP/EIP. They affect Supermicro BIOS in the Denverton platform. Supermicro is not aware of any public announcements or malicious use of these vulnerabilities that are described in this advisory.
- CVE-2020-8738
- CVE-2024-44075
Intel Platform Update (IPU) Update 2024.3, August 2024
This update applies to the X11, X12, and X13 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-01038 – 2024.2 IPU - Intel® Core™ Ultra Processor Stream Cache Advisory
- INTEL-SA-01046 – 2024.2 IPU - Intel® Processor Stream Cache Advisory
- INTEL-SA-00999 – 2024.3 IPU - Intel® Chipset Firmware Advisory
- INTEL-SA-01083 – 2024.3 IPU - SMI Transfer Monitor Advisory
- INTEL-SA-01100 – 2024.3 IPU - Intel® Xeon® Processor Advisory
- INTEL-SA-01118 – 2024.3 IPU - 3rd Generation Intel® Xeon® Scalable Processor Advisory
- INTEL-SA-01103 – 2024.3 IPU - Intel® Processor RAPL Interface Advisory
AMD Security Vulnerabilities, August 2024
This update applies to the H11, H12 and H13 families of products powered by 1st/2nd/3rd/4th Gen AMD EPYC™ Processors. This update also applies to M11/M12 and H13 family of products powered by Ryzen™ Threadripper™ processor. Potential vulnerabilities in various platform components were discovered and have been mitigated in AMD EPYC™ and AMD Ryzen™ AGESA™ PI packages.
- AMD-SB-4004 – AMD Client Vulnerabilities – August 2024
- AMD-SB-3003 – AMD Server Vulnerabilities – August 2024
AMD Security Bulletin AMD-SB-7014, August 2024
Supermicro is aware of the security vulnerability where an attacker with root access may modify the configuration of System Management Mode (SMM) even when SMM Lock is enabled. This issue affects AMD EPYC™ 1st, 2nd, 3rd and 4th Gen Processors and H11, H12, and H13 generations of products.
- CVE-2023-31315
AMD Security Bulletin AMD-SB-3011, August 2024
Supermicro is aware of the security issue where a malicious hypervisor may be able to decrypt the memory of a Secure Encrypted Virtualization–Secure Nested Paging (SEV-SNP) guest VM after it is decommissioned. This issue affects AMD EPYC™ 3rd and 4th Gen Processors. motherboards. This vulnerability affects BIOS in Supermicro H12 and H13 products.
- CVE-2023-31355
- CVE-2024-21978
- CVE-2024-21980
PKFAIL: Vulnerability in Supermicro BIOS firmware, July 2024
Supermicro has fixed the security vulnerability issue known as “PKFAIL”. This new vulnerability may allow malicious actors to launch advanced firmware-level threats from an operating system. It was determined that some Supermicro products used insecure Platform Keys (PK) which represent the Root of Trust for BIOS. These insecure keys were generated by American Megatrends International (AMI), and they were supplied as a reference example to Supermicro.
View detailsOpenSSH “regreSSHion” Vulnerability, July 2024
A security vulnerability with the critical signal handler race condition in OpenSSH, known as “regreSSHion” has been discovered in the BMC firmware of select Supermicro motherboards. This vulnerability may result in unauthenticated remote code execution (RCE) with root privileges.
- CVE-2024-6387
BIOS Vulnerabilities, July 2024
Supermicro is aware of potential vulnerabilities in the BIOS firmware. These vulnerabilities affect select X11 motherboards. Supermicro is not aware of any public announcements or malicious use of these vulnerabilities that are described in this advisory.
- CVE-2024-36432
- CVE-2024-36433
- CVE-2024-36434
Vulnerability in Supermicro BMC IPMI firmware, July 2024
A security issue has been discovered in select Supermicro motherboards. This issue affects the web server component of their BMC. This potential vulnerability in Supermicro BMC may come from a buffer overflow in the “GetValue” function of the firmware that is caused by a lack of checking the input value.
- CVE-2024-36435
AMD Security Bulletin AMD-SB-1041, June 2024
Supermicro is aware of the potential weakness in AMD SPI protection features. This issue affects AMD EPYC™ 1st, 2nd and 3rd Gen Processor motherboards. This vulnerability affects BIOS in Supermicro H11 and H12 products.
- CVE-2022-23829
AMD Security Bulletin AMD-SB-4007, May 2024
Supermicro is aware of the Memory leak vulnerabilities in AMD DXE (Drive Execution Environment) driver in Server and Client desktop and mobile APUs/CPUs may allow a highly privileged user to obtain sensitive information. This issue affects AMD EPYC™ 3rd Gen Processors. motherboards. This vulnerability affects BIOS in Supermicro H12 products.
- CVE-2023-20594
- CVE-2023-20597
Intel Platform Update (IPU) Update 2024.2, May 2024
This update applies to the X13 family of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-01036 – 2024.2 IPU - Intel® TDX Module Software Advisory
- INTEL-SA-01051 – 2024.2 IPU - Intel® Processor Advisory
- INTEL-SA-01052 – 2024.2 IPU - Intel® Core™ Ultra Processor Advisory
Vulnerabilities in Supermicro BMC firmware, April 2024
Several security vulnerabilities have been discovered in select Supermicro boards. These issues (cross site scripting and command injection) may affect the web server component of Supermicro BMC IPMI (Web UI). An updated BMC firmware had been created to mitigate these potential vulnerabilities.
- SMC-2024010010 (CVE: CVE-2024-36430)
- SMC-2024010011 (CVE: CVE-2024-36431)
- SMC-2024010012 (CVE: CVE-2023-33413)
Intel Platform Update (IPU) Update 2024.1 and INTEL-TA-00986, March 2024
This update applies to the X11, X12, and X13 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00898 – 2024.1 IPU - Intel® Atom® Processor Advisory
- INTEL-SA-00923 – 2024.1 IPU - Intel® Chipset Software and SPS Advisory
- INTEL-SA-00929 – 2024.1 IPU - BIOS Advisory
- INTEL-SA-00950 – 2024.1 IPU OOB - Intel® Processor Advisory
- INTEL-SA-00960 – 2024.1 IPU - Intel® Xeon® Processor Advisory
- INTEL-SA-00972 – 2024.1 IPU - Intel® Processor Bus Lock Advisory
- INTEL-SA-00982 – 2024.1 IPU - Intel® Processor Return Predictions Advisory
- INTEL-SA-00986 – 4th Gen Intel® Xeon® Processor Advisory
- INTEL-SA-01045 – 2024.1 IPU OOB - Intel® Xeon® D Processor Advisory
AMD Security Bulletin AMD-SB-7009, February 2024
Supermicro is aware of the AMD Processor Vulnerabilities. This issue affects AMD EPYC™ 1st Gen, AMD EPYC™ 2nd Gen, AMD EPYC™ 3rd Gen and 4th Gen Processors. This vulnerability affects Supermicro select H11, H12 and select H13 motherboards.
- CVE-2023-20576
- CVE-2023-20577
- CVE-2023-20579
- CVE-2023-20587
AMD Security Bulletin AMD-SB-3007, February 2024
Supermicro is aware of the SEV-SNP Firmware Vulnerabilities. This issue affects AMD EPYC™ 3rd Gen and 4th Gen Processors. This vulnerability affects Supermicro select H12 and select H13 motherboards.
- CVE-2023-31346
- CVE-2023-31347
PixieFAIL Vulnerability, January 2024
Supermicro is aware of a potential vulnerability known as “PixieFAIL” in the BIOS firmware. Multiple vulnerabilities were discovered in the TCP/IP stack (NetworkPkg) of Tianocore EDKII, an open source implementation of UEFI. These nine vulnerabilities that if exploited via network can lead to remote code execution, DoS attacks, DNS cache poisoning, and/or potential leakage of sensitive information. PixieFAIL affects Supermicro BIOS in select X11, X12, H11, H12, H13 and R12 products. Supermicro is not aware of any public announcements or malicious use of these vulnerabilities that is described in this advisory.
- CVE-2023-45229
- CVE-2023-45230
- CVE-2023-45231
- CVE-2023-45232
- CVE-2023-45233
- CVE-2023-45234
- CVE-2023-45235
- CVE-2023-45236
- CVE-2023-45237
LogoFAIL Vulnerability, December 2023
Supermicro is aware of a potential vulnerability known as “LogoFAIL” in the BIOS firmware. Improper input validation in an image parser library used by BIOS may allow a privileged user to potentially enable escalation of privilege via local access. LogoFAIL affects Supermicro BIOS in select X11, X12, X13, H11, M12 and R12 products. Supermicro is not aware of any public announcements or malicious use of these vulnerabilities that is described in this advisory.
- CVE-2023-39538
- CVE-2023-39539
Vulnerabilities in Supermicro BMC IPMI Firmware, December 2023
- CVE-2023-33411: IPMI BMC SSDP/UPnP web server directory traversal and iKVM access allowing the rebooting of the BIOS
- CVE-2023-33412: IPMI BMC administrative web interface virtual floppy/USB remote command execution
- CVE-2023-33413: IPMI BMC devices use hardcoded configuration file encryption keys, allowing the attacker to craft and upload a malicious configuration file packages to gain remote command execution.
AMD Security Bulletin AMD-SB-3005
Supermicro is aware of the AMD INVD Instruction security vulnerability. This issue affects 1st Gen AMD EPYC™ Processors (SEV and SEV-ES), 2nd Gen AMD EPYC™ Processors (SEV and SEV-ES), and 3rd Gen AMD EPYC™ Processors (SEV, SEV-ES, SEV-SNP). This vulnerability affects Supermicro H11 and H12 motherboards.
- CVE-2023-20592
Intel Platform Update (IPU) Update 2023.4 and INTEL-SA-00950, November 2023
This update applies to the X11, X12, and X13 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00924 – 2023.4 IPU – BIOS Advisory
- INTEL-SA-00950 – Intel® Processor Advisory
AMD Security Vulnerabilities, November 2023
This update applies to the H11, H12 and H13 families of products powered by 1st/
- AMD-SN-4002 - AMD Client Vulnerabilities – November 2023
- AMD-SN-3002 - AMD Server Vulnerabilities – November 2023
Vulnerabilities in Supermicro BMC IPMI firmware
Several security vulnerabilities have been discovered in select Supermicro boards. These issues (cross site scripting and command injection) may affect the web server component of Supermicro BMC IPMI (Web UI). An updated BMC firmware had been created to mitigate these potential vulnerabilities.
- CVE-2023-40289
- CVE-2023-40284
- CVE-2023-40287
- CVE-2023-40288
- CVE-2023-40290
- CVE-2023-40285
- CVE-2023-40286
Variable Modification Due to Stack Overflow
A potential vulnerability was found in the Supermicro BIOS firmware. An attacker could exploit this vulnerability in the Supermicro motherboards by manipulating a variable to potentially hijack the control flow, allowing attackers with the kernel level privileges to escalate their privileges and potentially execute arbitrary code.
- CVE-2023-34853
AMD Security Bulletin AMD-SB-7005
Supermicro is aware of the Return Address Predictor issue, also known as "INCEPTION." This issue affects AMD EPYC™ 3rd Gen and 4th Gen Processors. This vulnerability affects Supermicro select H12 and select H13 motherboards.
- CVE-2023-20569
Intel Platform Update (IPU) Update 2023.3, August 2023
This update applies to the X11, X12, and X13 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00783 – 2023.2 IPU – Intel® Chipset Firmware Advisory
- INTEL-SA-00813 – 2023.2 IPU – BIOS Advisory
- INTEL-SA-00828 – 2023.2 IPU – Intel® Processor Advisory
- INTEL-SA-00836 – 2023.2 IPU – Intel® Xeon® Scalable Processors Advisory
- INTEL-SA-00837 – 2023.2 IPU – Intel® Xeon® Processor Advisory
AMD Security Bulletin AMD-SB-7008
Supermicro is aware of the cross-process information leak, also known as "Zenbleed". This issue affects AMD EPYC™ 7002 Processors also known as AMD “Zen 2” processors. This vulnerability affects Supermicro H11 and H12 motherboards.
- CVE-2023-20593
Shell injection in the SMTP notifications
Vulnerability in the select supermicro boards may affect SMTP notification configurations. The vulnerability may allow unauthenticated bad actors to control user inputs such as the subject in the alert settings which may lead to an arbitrary execution of code.
- CVE-2023-35861
Reflective Denial-of-Service (DoS) Amplification Vulnerability in Service Location Protocol SLP
The Service Location Protocol (SLP) allows an unauthenticated, remote attacker to register arbitrary services. This could allow the attacker to use spoofed UDP traffic to conduct a denial-of-service (DoS) attack with a significant amplification factor.
- CVE-2023-29552
Media Information: Intel BootGuard OEM private keys have potentially been compromised, May 2023
Based on the analysis of how Supermicro generates and uses private keys, Supermicro products are not affected.
Intel Platform Update (IPU) Update 2023.2, May 2023
This update applies to the X11, X12, and X13 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00807 – 2023.2 IPU – BIOS Advisory
AMD Security Vulnerabilities, May 2023
This update applies to the H11, H12 and H13 families of products powered by 1st/2nd/3rd/4th Gen AMD EPYC™ Processors. This update also applies to M12 family of products powered by Ryzen™ Threadripper™ processor. Potential vulnerabilities in various platform components were discovered and have been mitigated in AMD EPYC™ and AMD Ryzen™ AGESA™ PI packages.
- AMD-SN-4001 - AMD Client Vulnerabilities – May 2023
- AMD-SN-3001 - AMD Server Vulnerabilities – May 2023
SuperDoctor5 Advisory, March 2023
Researchers have identified a vulnerability in Supermicro SuperDoctor5 (SD5) that may allow any authenticated user on the web interface to remotely execute arbitrary commands on the system where SuperDoctor5 (SD5) is installed.
- CVE-2023-26795
Intel Platform Update (IPU) Update 2023.1, February 2023
This update applies to the X11, X12, and X13 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00700 – 2023.1 IPU – Intel® Atom® and Intel® Xeon® Scalable Processors Advisory
- INTEL-SA-00717 – 2023.1 IPU – BIOS Advisory
- INTEL-SA-00718 – 2023.1 IPU – Intel® Chipset Firmware Advisory
- INTEL-SA-00730 – 2023.1 IPU – 3rd Gen Intel® Xeon® Scalable Processors Advisory
- INTEL-SA-00738 – 2023.1 IPU – Intel® Xeon® Processor Advisory
- INTEL-SA-00767 – 2023.1 IPU – Intel® Processor Advisory
Voltage Regulator Module (VRM) and Inter-Integrated Circuit (I²C) Overvolting/Undervolting, January 2023
Researchers have identified a vulnerability in The Board Management Controller (BMC) which may allow changes to the voltage to be outside the specified operating range for the CPU and therefore, affect normal computations.
- CVE-2022-43309
AMD Security Vulnerabilities, January 2023
This update applies to the H11 and H12 families of products powered by 1st/2nd/3rd/4th Gen AMD EPYC™ Processors. This update also applies to M12 family of products powered by Ryzen™ Threadripper™ processor. Potential vulnerabilities in various platform components were discovered and have been mitigated in AMD EPYC™ and AMD Ryzen™ AGESA™ PI packages.
- AMD-SN-1031 - AMD Client Vulnerabilities – January 2023
- AMD-SN-1032 - AMD Server Vulnerabilities – January 2023
Intel Platform Update (IPU) Update 2022.3, November 2022
This update applies to the X11, and X12 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00610 - 2022.3 IPU – Intel® Chipset Firmware Advisory
- INTEL-SA-00668 - 2022.2 IPU – BIOS Advisory
OpenSSL Advisory, November 2022
OpenSSL versions from 3.x through 3.0.6 are found vulnerable to a high severity security vulnerability that can lead to crash or unexpected behavior. Supermicro products are not affected by this OpenSSL vulnerability.
- CVE-2022-3786
- CVE-2022-3602
Microsoft Windows Secure Boot Bypass, August 2022
Researchers have identified several vulnerabilities in Microsoft’s third-party bootloaders that can affect all computer systems using x64 UEFI Secure Boot.
- CVE-2022-34301
- CVE-2022-34302
- CVE-2022-34303
Intel Platform Update (IPU) Update 2022.2, August 2022
This update applies to the X11, and X12 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00657 - 2022.2 IPU – Intel® Processor Advisory
- INTEL-SA-00669 - 2022.2 IPU – Intel® Chipset Firmware Advisory
- INTEL-SA-00686 - 2022.2 IPU – BIOS Advisory
Intel Platform Update (IPU) Update 2022.1, June 2022
This update applies to the X10, X11, and X12 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00601 - 2022.1 IPU – BIOS Advisory
- INTEL-SA-00613 - 2022.1 IPU – Intel® Boot Guard and Intel® TXT Advisory
- INTEL-SA-00614 - 2022.1 IPU – Intel® SGX Advisory
- INTEL-SA-00615 - 2022.1 IPU – Intel® Processors MMIO Stale Data Advisory
- INTEL-SA-00616 - 2022.1 IPU – Intel® Xeon Advisory
- INTEL-SA-00617 - 2022.1 IPU – Intel® Processor Advisory
AMD Security Vulnerabilities, May 2022
This update applies to the H11 and H12 families of products powered by 1st/2nd/3rd Gen AMD EPYC™ Processors. This update also applies to M12 family of products powered by Ryzen™ Threadripper™ processor. Potential vulnerabilities in various platform components were discovered and have been mitigated in AMD EPYC™ and AMD Ryzen™ AGESA™ PI packages.
- AMD-SN-1027 - AMD Client Vulnerabilities – May 2022
- AMD-SN-1028 - AMD Server Vulnerabilities – May 2022
Intel Platform Update (IPU) Update 2021.2, February 2022
This update applies to the X10, X11, and X12 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00470 - 2021.2 IPU – Intel® Chipset Firmware Advisory
- INTEL-SA-00527 - 2021.2 IPU – BIOS Advisory
- INTEL-SA-00532 - 2021.2 IPU – Intel® Processor Breakpoint Control Flow Advisory
- INTEL-SA-00561 - 2021.2 IPU – Intel® Processor Advisory
- INTEL-SA-00589 - 2021.2 IPU – Intel Atom® Processor Advisory
Supermicro’s response to Apache Log4j vulnerability
Supermicro is aware and joins the industry to mitigate the exposure caused by the high-priority CVE-2021-44228 (Apache Log4j 2) issue, also coined as “Log4Shell”, the CVE-2021-45046 (Apache Log4j 2) issue, and the CVE-2021-45105 (Apache Log4j 2) issue. Supermicro is also aware of the CVE-2021-4104 and CVE-2019-17571 issues for Apache Log4j 1.2.
Most Supermicro applications are not impacted by these five vulnerabilities. The only impacted application is Supermicro Power Manager (SPM). The issue will be addressed in a new version of Supermicro Power Manager (SPM) with the release pending ASAP. SPM will come with Log4j version 2.17.0.
Log4j 2
- CVE-2021-44228
- CVE-2021-45046
- CVE-2021-45105
Log4j 1.2
- CVE-2019-17571
- CVE-2021-4104
Intel Platform Update (IPU) Update 2021.2, November 2021
This update applies to the X10, X11, and X12 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00528 - 2021.2 IPU – Intel® Atom® Processor Advisory
- INTEL-SA-00562 - 2021.1 IPU – BIOS Reference Code Advisory
AMD Security Vulnerabilities, November 2021
This update applies to the H11 and H12 families of products powered by 1st/2nd/3rd Gen AMD EPYC™ Processors. Potential vulnerabilities in various platform components were discovered and have been mitigated in AMD EPYC™ AGESA™ PI packages.
- AMD-SN-1021 - AMD Server Vulnerabilities – November 2021
Intel Security Advisory Intel-SA-00525, July 2021
- INTEL-SA-00525 – Intel BSSA (BIOS Shared SW Architecture) DFT Advisory
Intel-SA-00525 Security Advisory does not affect Supermicro BIOS.
View detailsIntel Platform Update (IPU) Update 2021.1, June 2021
This update applies to the X10, X11, and X12 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00442 - 2021.1 IPU – Intel VT-d Advisory
- INTEL-SA-00459 - 2021.1 IPU – Intel-CSME-SPS-TXE-DAL-AMT-Advisory
- INTEL-SA-00463 - 2021.1 IPU – BIOS Advisory
- INTEL-SA-00464 - 2021.1 IPU – Intel Processor Advisory
- INTEL-SA-00465 - 2021.1 IPU – Intel Processor Advisory
Supermicro’s response to Trickboot vulnerability, March 2021
Supermicro is aware of the Trickboot issue which is observed only with a subset of the X10 UP motherboards. Supermicro will be providing a mitigation for this vulnerability.
TrickBoot is a new functionality within the TrickBot malware toolset capable of discovering vulnerabilities and enabling attackers to read/write/erase the BIOS on the device.
Read MoreBIOS detects GRUB2 boot loader vulnerability in Linux OS, November 2020
A flaw was found in GRUB2, prior to version 2.06. An attacker may use the GRUB2 flaw to hijack and tamper the GRUB verification process. BIOS will detect this condition and halt the boot with an error message.
- CVE-2020-10713
Intel Platform Update (IPU) Update 2020.2, November 2020
This update applies to the X10, X11, and X12 families of products powered by Intel Xeon® and other Intel processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00358 – 2020.2 IPU – BIOS Advisory
- INTEL-SA-00391 – 2020.2 IPU – Intel® CSME, SPS, TXE, and AMT Advisory
- INTEL-SA-00389 – 2020.2 IPU – Intel® RAPL Advisory
- INTEL-SA-00390 – Intel BIOS Platform Sample Code Advisory
Intel Monthly September Security Update, September 2020
This update applies to the X11 and X12 families of products powered by Intel Core® processors. Intel Monthly September Security Update combines the delivery of security updates that may have been previously provided individually.
Please note that X10 family of products is not affected by this announcement.
- Intel-SA-00404 – Intel® AMT and Intel® ISM Advisory
Intel Platform Update (IPU) Update 2020.1, June 2020
This update applies to the X10 and X11 families of products powered by Intel Xeon® processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- Intel-SA-00295 – Intel® CSME, SPS, TXE, AMT and DAL Advisory
- Intel-SA-00320 – Special Register Buffer Data Sampling Advisory
- Intel-SA-00322 – 2020.1 IPU BIOS Advisory
- Intel-SA-00329 – Intel® Processors Data Leakage Advisory
- Intel-SA-00260 – (updated) Intel® Processor Graphics 2019.2 QSR Update Advisory
Lot 9 of ErP (Eco-design) Compliance
Lot 9 regulations are a new set of product standards that deal with data storage devices such as enterprise-level servers. Learn how Supermicro meets European Union (EU) Eco-design requirements for servers and storage products as part of Lot 9 Compliance.
View detailsIntel Monthly February Security Update, February 2020
This update applies to the X11 families of products powered by Intel Core® processors. Intel Monthly February Security Update combines the delivery of security updates that may have been previously provided individually.
- Intel-SA-00307 – Escalation of Privilege, Denial of Service, Information Disclosure
Intel BIOS Update, INTEL-SA-00329, January 2020
- Intel-SA-00329 – Intel® Processors Data Leakage Advisory
Intel Monthly December Security Update, December 2019
This update applies to the X10, and X11 families of products powered by Intel Xeon® processors. Intel Monthly December Security Update combines the delivery of security updates that may have been previously provided individually.
- Intel-SA-00289 – Intel® Processors Voltage Settings Modification Advisory
- Intel-SA-00317 – Unexpected Page Fault in Virtualized Environment Advisory
Intel Platform Update (IPU) Update 2019.2, November 2019
This update applies to the X10, and X11 families of products powered by Intel Xeon® processors. Intel Platform Update (IPU) combines the delivery of security updates that may have been previously provided individually.
- Intel-SA-00164 – Intel® Trusted Execution Technology 2019.2 IPU Advisory
- Intel-SA-00219 – Intel® SGX 2019.2 with Intel® Processor Graphics IPU Update Advisory
- Intel-SA-00220 – Intel® SGX and Intel® TXT Advisory
- Intel-SA-00240 – Intel CPU Local Privilege Escalation Advisory
- Intel-SA-00241 – Intel® CSME, Server Platform Services, Trusted Execution Engine, Intel® Active Management Technology and Dynamic Application Loader 2019.2 IPU Advisory
- Intel-SA-00254 – Intel® System Management Mode 2019.2 IPU Advisory
- Intel-SA-00260 – Intel® Processor Graphics 2019.2 IPU Advisory
- Intel-SA-00270 – TSX Transaction Asynchronous Abort Advisory
- Intel-SA-00271 – Voltage Modulation Technical Advisory
- Intel-SA-00280 – BIOS 2019.2 IPU Advisory
BMC/IPMI Security Vulnerability Update September 3, 2019
Researchers have identified several security related issues on the Virtual Media function of Supermicro BMCs that requires a BMC firmware update to address.
CVE-2019-16649
CVE-2019-16650
AMD Security Vulnerability: Secure Encrypted Virtualization Invalid ECC Curve Points (SEV ECC) in Linux Operating System vulnerability
CVE-2019-9836
View detailsIntel Security Vulnerability regarding Rowhammer style attack to leak information from certain DRAM modules
Intel-SA-00247 (CVE-2019-0174)
View detailsIntel Quarterly Security Release (QSR) Update 2019.1, May 2019
This update applies to the X8, X9, X10, and X11 families of products powered by Intel Xeon® processors. Quarterly Security Release (QSR) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00213 (CVE-2019-0089, CVE-2019-0090, CVE-2019-0086, CVE-2019-0091, CVE-2019-0092, CVE-2019-0093, CVE-2019-0094, CVE-2019-0096, CVE-2019-0097, CVE-2019-0098, CVE-2019-0099, CVE-2019-0153, CVE-2019-0170)
- INTEL-SA-00223 BIOS Not Affected
- INTEL-SA-00233(CVE-2018-12126, CVE-2018-12127, CVE-2018-12130, CVE-2019-11091)
BIOS updates for these issues are rolling out now. View the details below for impacted products and necessary BIOS updates.
Intel Quarterly Security Release (QSR) Update 2018.4, March 2019
This update applies only to the X11 family of products powered by Intel Xeon® processors. Quarterly Security Release (QSR) combines the delivery of security updates that may have been previously provided individually.
- INTEL-SA-00185 (CVE-2018-12188, CVE-2018-12189, CVE-2018-12190, CVE-2018-12191, CVE-2018-12192, CVE-2018-12199, CVE-2018-12198, CVE-2018-12200, CVE-2018-12187, CVE-2018-12196, CVE-2018-12185, CVE-2018-12208)
- INTEL-SA-00191 (CVE-2018-12201, CVE-2018-12202, CVE-2018-12203, CVE-2018-12205, CVE-2018-12204)
"Spoiler": New research Article on speculative execution in Intel processors
View detailsBaseboard Management Controller (BMC) Security Vulnerabilities regarding systems using the ASPEED AST2400 and AST2500 system-on-chips (SoCs)
- CVE-2019-6260
Spectre and Meltdown Side Channel Speculative Execution
- Intel SA-00115 (CVE-2018-3639, CVE-2018-3640)
- Intel-SA-00088 (CVE-2017-5715, CVE-2017-5753, CVE-2017-5754)
- Intel-SA-00161 (CVE-2018-3615, CVE-2018-3620, CVE-2018-3646)
Intel Security Vulnerabilities Regarding Intel® Management Engine (ME), Intel® Server Platform Services (SPS), and Intel® Trusted Execution Engine (TXE)
- Intel-SA-00086 (CVE-2017-5705, CVE-2017-5708, CVE-2017-5711, CVE-2017-5712, CVE-2017-5706, CVE-2017-5709, CVE-2017-5707, CVE-2017-571000)
BIOS/BMC Firmware Security updates prior to 2017
See Firmware Fixes to Common Vulnerabilities and Exposures published prior to 2017.
Supermicro pro-actively works with the security community to identify and strengthen security across our product line. Please find solutions to CVEs published on Supermicro firmware.
View detailsCommon Security FAQs: Choose category "Security"
Report a Product Security Issue
If you encountered a security issue with a Supermicro product, please send an e-mail to secure@supermicro.com with the following details:
- Product name/SKU
- Detailed report on the vulnerability
- Instructions to reproduce
- Any relevant CVEs
Please do not include any sensitive or confidential information in clear text emails – use PGP Key to encrypt your message. Supermicro Product Security Team will review your report and contact you to jointly resolve the issue.
View detailsGet connected with product security updates from Supermicro
Subscribe today
In order to initiate a subscription to receive future Supermicro Security alerts please take the following steps:
1. Go to the upper right portion of your screen and sign in or create a Single Sign-On (SSO) account:
2. Select “Manage Email Preferences”
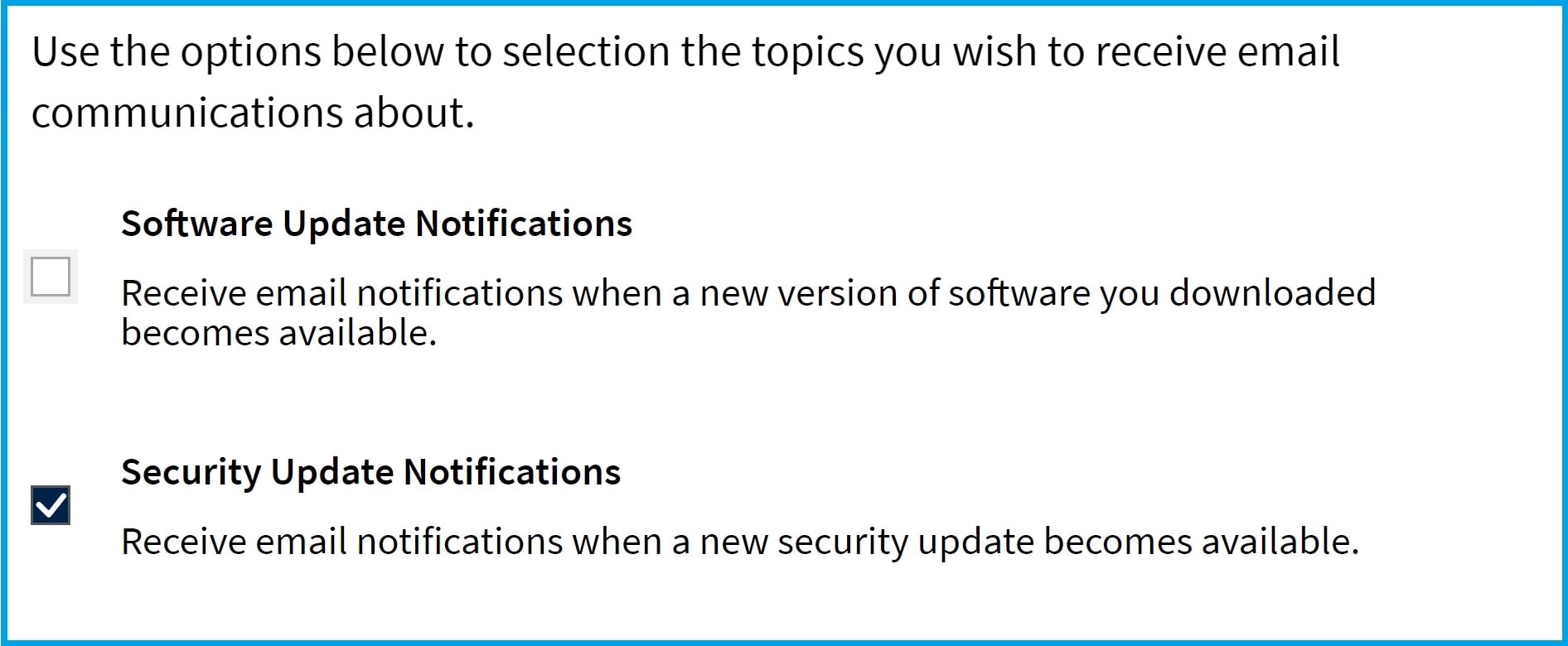
3.Check “Security Update Notifications”
- Effective Date
- Last Updated
Overview
At Supermicro, we are committed to maintaining the security and integrity of our products and services. This End-of-Life (EOL) Security Policy outlines how we manage security issues for products that have reached their EOL status, ensuring transparency and helping customers plan for upgrades and transitions.
What Is End-of-Life (EOL)?
A product or service is considered EOL when we officially announce that it will no longer be actively developed, maintained, or enhanced.
Security Support Timeline
We understand that transitioning from legacy products takes time. To support our customers:
- Security issues with Critical (9.0 - 10.0) and High (7.0 - 8.9) severity will continue to be supported for three (3) years following the EOL announcement date.
- During this period, we will evaluate reported vulnerabilities and may issue patches or mitigations based on severity and impact.
- After the three-year window, no further security updates or investigations will be provided.
Exceptions
Extended security support beyond the standard three-year period may be available under a separate agreement. Please contact Supermicro to discuss options.
Contact Us
For questions or concerns about this policy, please reach out to our Security Team at: secure@supermicro.com

